

What is Biometric Authentication and How Does It Work?
Biometric authentication can easily be explained as a way to verify someone’s identity using physical or behavioral traits that are unique to them like a fingerprint, facial features, or even how they walk or type.
VELLIS NEWS
19 Aug 2025
By Vellis Team
Vellis Team
Automate your expense tracking with our advanced tools. Categorize your expenditures
Related Articles

Vellis News
3 October 2025
Open Banking API: What is it?
If you’ve been following the digital finance space, chances are you’ve heard about open banking APIs. But what exactly are they, and why are they so important?

Vellis News
9 October 2025
Does Opening a Bank Account Affect Credit Score
A credit score shows how responsibly you borrow and repay money. Lenders and landlords use it to gauge trustworthiness. Opening a regular checking or savings account doesn’t affect your score, but accounts with overdraft protection or credit checks might cause a small inquiry.

Vellis News
18 December 2025
ACH Debit vs Direct Debit: What’s the Difference?
ACH debit and direct debit are both bank-based payment methods that let businesses pull funds directly from a customer’s account after authorization. When comparing ACH debit vs direct debit, the confusion usually comes from terminology rather than how the payments actually work. In this guide, we’ll break down how each method operates, how they differ […]
It’s become a popular choice for secure access, showing up everywhere from unlocking smartphones to protecting sensitive company data. Therefore, in this article, we’ll break down what biometric authentication is, how it works, the different types you might come across, its main benefits and risks, and the rules and regulations that surround its use.
What is Biometric Authentication?
Biometric authentication is a security process that confirms a person’s identity by using their unique physical or behavioral traits, such as fingerprints, facial structure, voice, or even typing patterns. These traits are difficult to replicate, making them a reliable method for secure access. It’s important to distinguish between authentication and identification: authentication verifies that you are who you say you are (e.g., unlocking your phone), while identification finds out who you are from a group (e.g., scanning a crowd for matches). It is important to note that biometric systems are often used alongside AML compliance tools to ensure that only verified individuals can access sensitive financial or personal data.
How Biometric Authentication Works
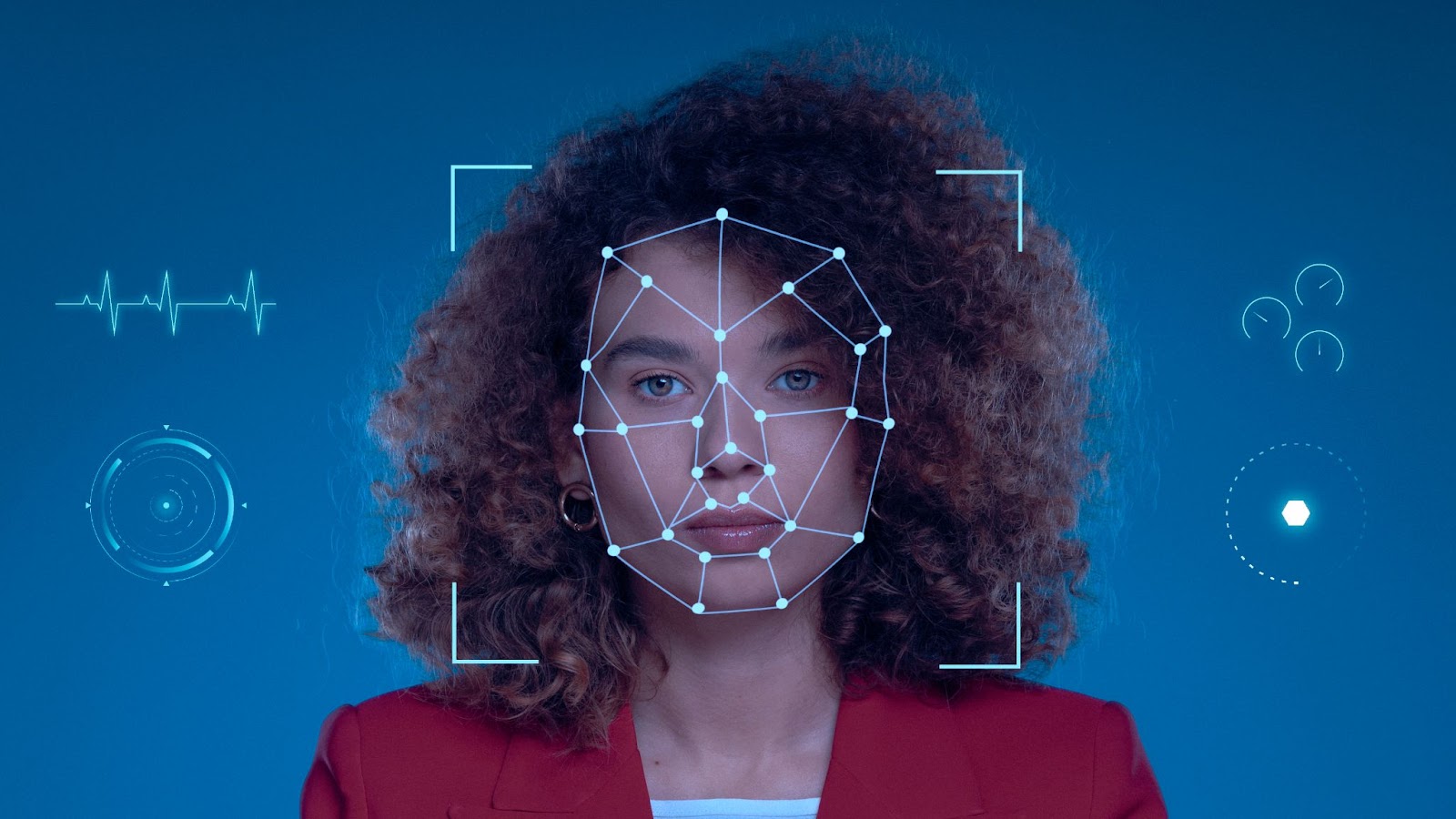
Biometric authentication starts with enrollment, where your unique trait, like a fingerprint or facial scan is captured and turned into a digital template. This data is then encrypted and stored, either on your device or a secure server. Later, when you try to log in, the system captures your biometric input again and compares it to the stored template. If it matches, access is granted. Some systems do all this on your device for extra privacy, while others send the data to a server for verification. Each method has its pros and cons. This secure approach is often combined with other tools to meet regulations, especially in financial systems where people might also ask, what is open banking, and how data is protected.
Types of Biometric Authentication
Biometric authentication comes in several forms, each using a different personal trait to verify who you are. Here are some of the main types:
- Fingerprint Recognition
Scans the unique patterns on your fingertip. It’s fast, reliable, and widely used in phones, laptops, and entry systems. - Facial Recognition
Uses the structure of your face, like the distance between your eyes or shape of your jaw, in order to verify identity. Common in smartphones and surveillance. - Iris and Retina Scans
Analyze the patterns in your eye. These methods are highly accurate but more common in high-security settings due to cost and complexity. - Voice Recognition
Identifies a person by their speaking style, pitch, and tone. Often used in customer service and phone-based access. - Behavioral Biometrics
Looks at how you type, swipe, or walk (gait). These patterns are hard to fake and useful for continuous authentication. - Emerging Technologies
Include vein pattern recognition, ear shape mapping, and even heartbeat rhythm. These are gaining attention for their uniqueness and potential value, especially for SME payment processors looking to enhance security without adding user friction.
Common Use Cases and Applications
In addition, biometric authentication is used across many areas to boost security and streamline access:
- Mobile Device Security – Unlocking phones or apps with Face ID or fingerprint scanners.
- Banking and Financial Services – Secure logins, transaction approvals, and fraud prevention.
- Healthcare – Verifying patient identity to ensure correct treatment and protect records.
- Border Control and Law Enforcement – Matching faces or fingerprints at checkpoints or in investigations.
- Enterprise Access Management – Controlling who can enter physical buildings or access sensitive systems at work.
Advantages of Biometric Authentication
Biometric authentication offers several key advantages. In the first place, it maximally provides a high level of security and accuracy since it relies on traits that are unique to each person. It’s also fast and convenient where users can access systems or devices in seconds without needing to remember anything. By eliminating the need for traditional passwords, it reduces the risk of forgotten credentials or weak password choices. Plus, because biometric traits are hard to fake or duplicate, it adds an extra layer of protection against unauthorized access.
Challenges and Risks of Biometrics
While biometric authentication offers strong security, it also comes with important challenges. One major concern is privacy, especially regarding how and where biometric data is stored. If this sensitive data is ever stolen in a breach, it can’t be changed like a password, raising the risk of permanent identity loss. Biometric systems can also produce false positives or false negatives, which may lead to access issues or security gaps. Another issue is accessibility, people with injuries, disabilities, or certain medical conditions might struggle to use fingerprint scanners or facial recognition tools. These risks make it essential to use biometrics carefully and combine them with other safeguards to ensure both security and fairness for all users.
Biometric Authentication and Data Privacy Laws

Biometric authentication is tightly regulated under several data privacy laws, including the GDPR in Europe, CCPA in California, and BIPA in Illinois. These laws recognize biometric data as sensitive personal information, meaning it must be handled with extra care. Companies are required to get informed consent before collecting any biometric data, and they must clearly explain how it will be used. Data minimization is also key, which means that only the necessary information should be collected. Rules also cover how the data is stored, how long it can be kept, and the proper way to delete it when no longer needed. These regulations are designed to protect users and reduce the risks tied to storing such personal and unchangeable data.
Comparing Biometrics with Other Authentication Methods
Biometrics differ from traditional authentication methods like passwords, PINs, and tokens because they rely on something unique to you, such as your physical or behavioral traits, rather than something you know or carry. Passwords and PINs can be forgotten, stolen, or guessed, while tokens can be lost or duplicated. Biometrics offer greater convenience since you don’t have to remember anything, but they also come with risks if biometric data is compromised. That’s why biometrics are often used as part of multi-factor authentication (MFA), combining something you are (biometrics) with something you know (password) or have (token). This balance improves security by adding layers, though it requires weighing convenience against control depending on the situation.
Future of Biometric Authentication
As it seems, the future of biometric authentication looks promising, with AI and machine learning playing a big role in making recognition faster and more accurate. What’s more, these technologies help systems better distinguish real users from fraudsters, even in tricky conditions. Biometrics are also becoming a key part of decentralized identity systems, giving individuals more control over their personal data without relying on central authorities. At the same time, biometric payment systems and smart devices are growing rapidly, allowing seamless and secure transactions with just a glance or a touch. Industry-wide standardization efforts, like FIDO2 and ISO standards, are helping ensure these technologies work smoothly across different platforms and devices, boosting security and user convenience worldwide.
FAQs
What is biometric authentication used for?
It is used to verify identity securely in phones, apps, banking, border control, and more.
What type of authentication is biometrics?
Biometrics is a form of something you are authentication, based on unique personal traits.
Is biometric authentication safer than passwords?
Yes, in most cases it’s safer, though it should be combined with other layers of security for best protection.
Can biometric data be stolen or hacked?
Yes, if stored insecurely on servers, biometric data can be targeted, and unlike passwords, it cannot be changed.
What is the most secure form of biometric authentication?
Iris or retina scans are often considered the most secure due to their uniqueness and difficulty to replicate.
References
Science Direct: Biometric Authentication
How Stuff Works: How Biometrics Works
https://science.howstuffworks.com/biometrics.htm
Spice Works: What Is Biometric Authentication? Definition, Benefits, and Tools
IBM: What is biometric authentication?
Related Articles

Vellis News
10 June 2025
What is Mobile Gaming? Everything You Need to Know
Mobile gaming means playing video games on phones, tablets, or handheld devices. These games range from simple puzzles to massive multiplayer experiences, playable anytime and anywhere.

Vellis News
18 February 2026
What Is Direct Debit and How Does It Work?
If you’ve ever paid a utility bill automatically, stayed subscribed to a streaming platform without thinking about monthly payments, or set up hands-free billing for insurance, you’ve likely encountered direct debit even if you didn’t realize it. So, what is direct debit, and why has it become such a widely used payment method across the […]

Vellis News
28 July 2025
How to Send Money Without a Bank Account?
Not everyone has access to a traditional bank account, but that doesn’t mean they’re excluded from financial transactions. It’s entirely possible to send money without a bank account safely and efficiently.
We use cookies to improve your experience and ensure our website functions properly. You can manage your preferences below. For more information, please refer to our Privacy Policy.
© 2025 Vellis Inc.Vellis Inc. is authorized as a Money Services Business by FINTRAC (Financial Transactions and Reports Analysis Centre of Canada) number M24204235. Vellis Inc. is a company registered in Canada, number 1000610768, headquartered at 30 Eglinton Avenue West, Mississauga, Ontario L5R3E7, Canada.